Make sure you have the service and integration already setup for AWS. Follow the link below on instructions of how to create integration and service
Create integration and service on our dashboard
We will create a SNS topic and add alarms on say EC2 servers which can be monitored eventually on Cloudwatch
Login to your AWS console and head straight to Simple Notification Service (SNS).
We will create a topic in SNS which will be available across AWS services.
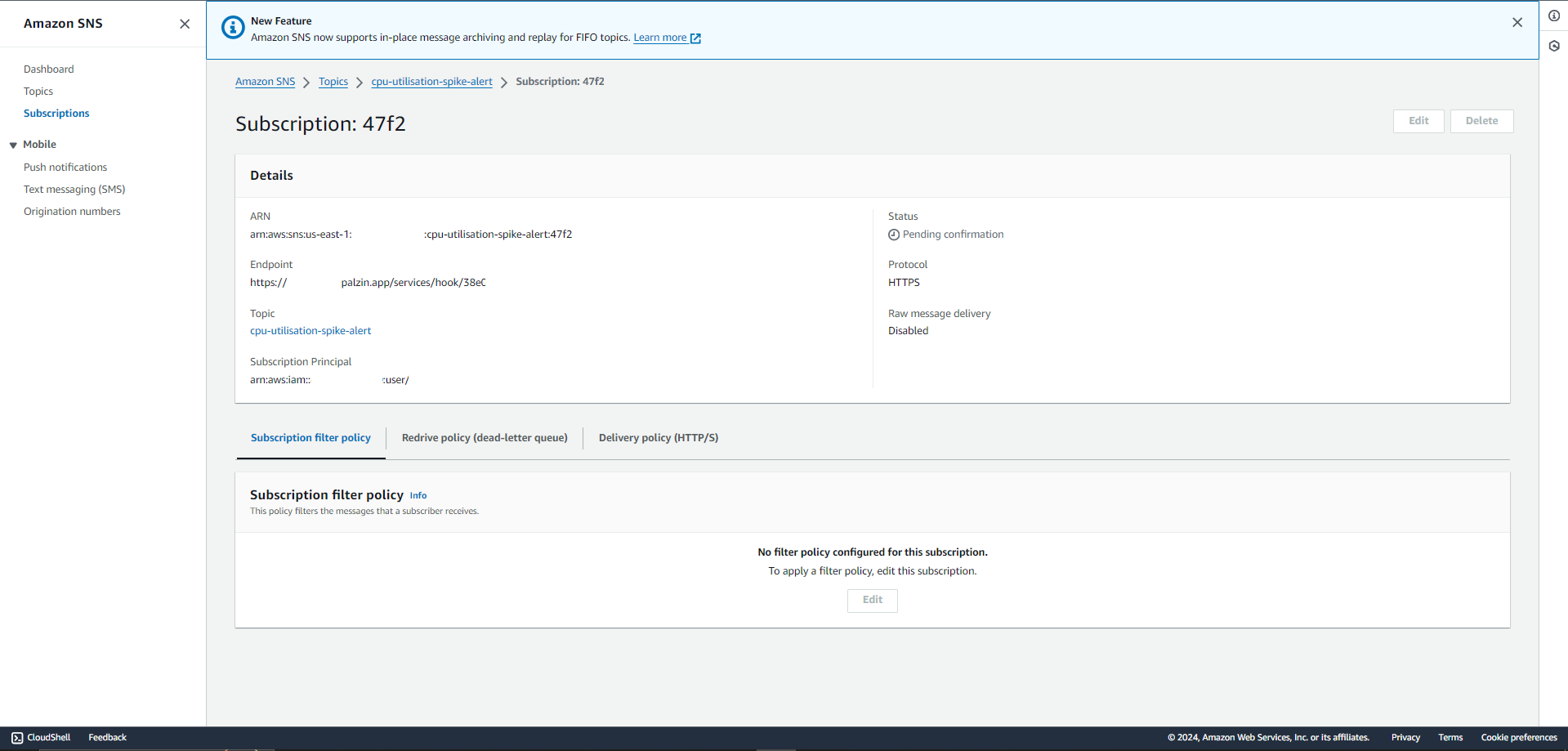
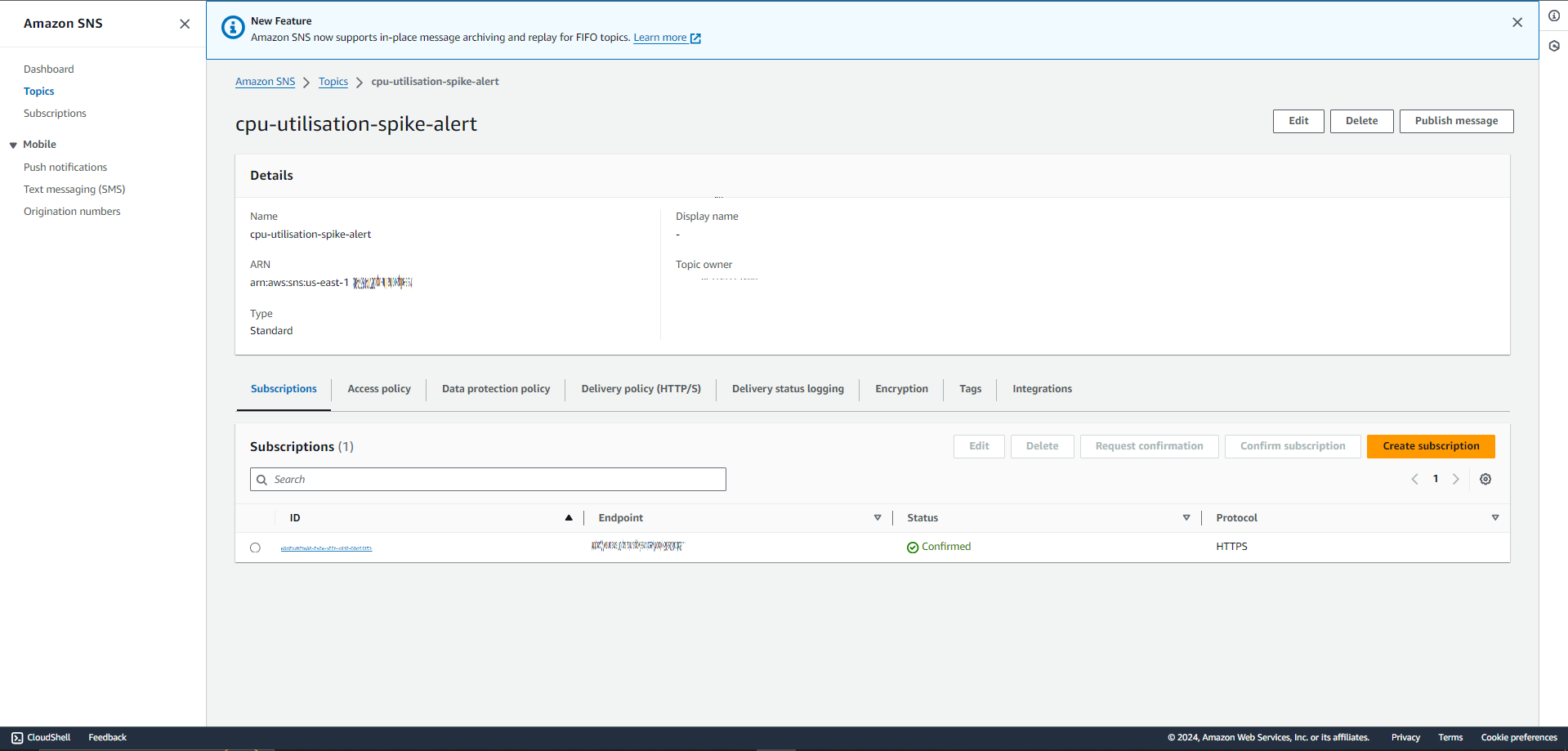
After your subscription is made, you will be taken to the topic's detail page. Refresh the page to make sure that the status will be confirmed for the subscription. If that fails to happen, you can click on the topic page and ask to request confirmation.
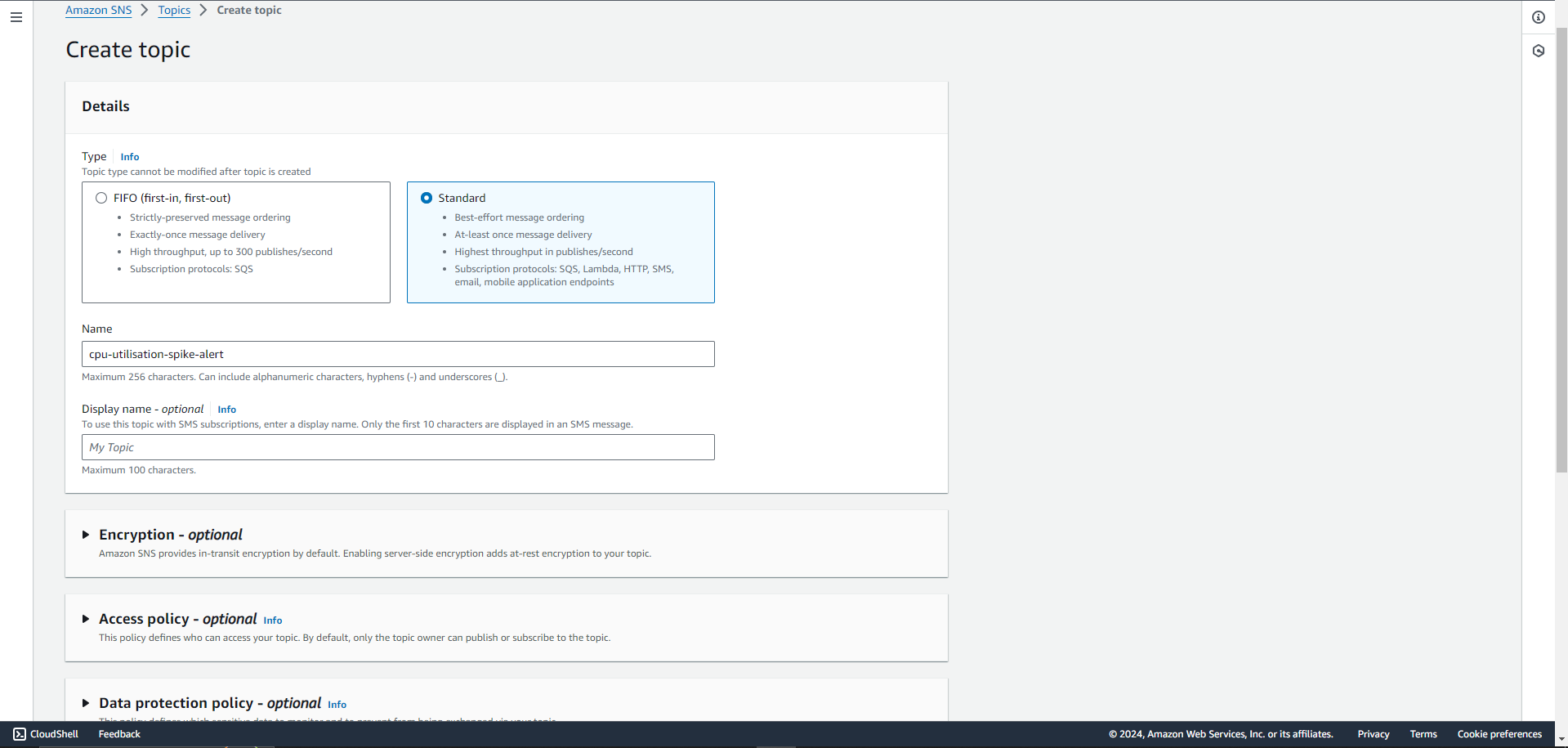
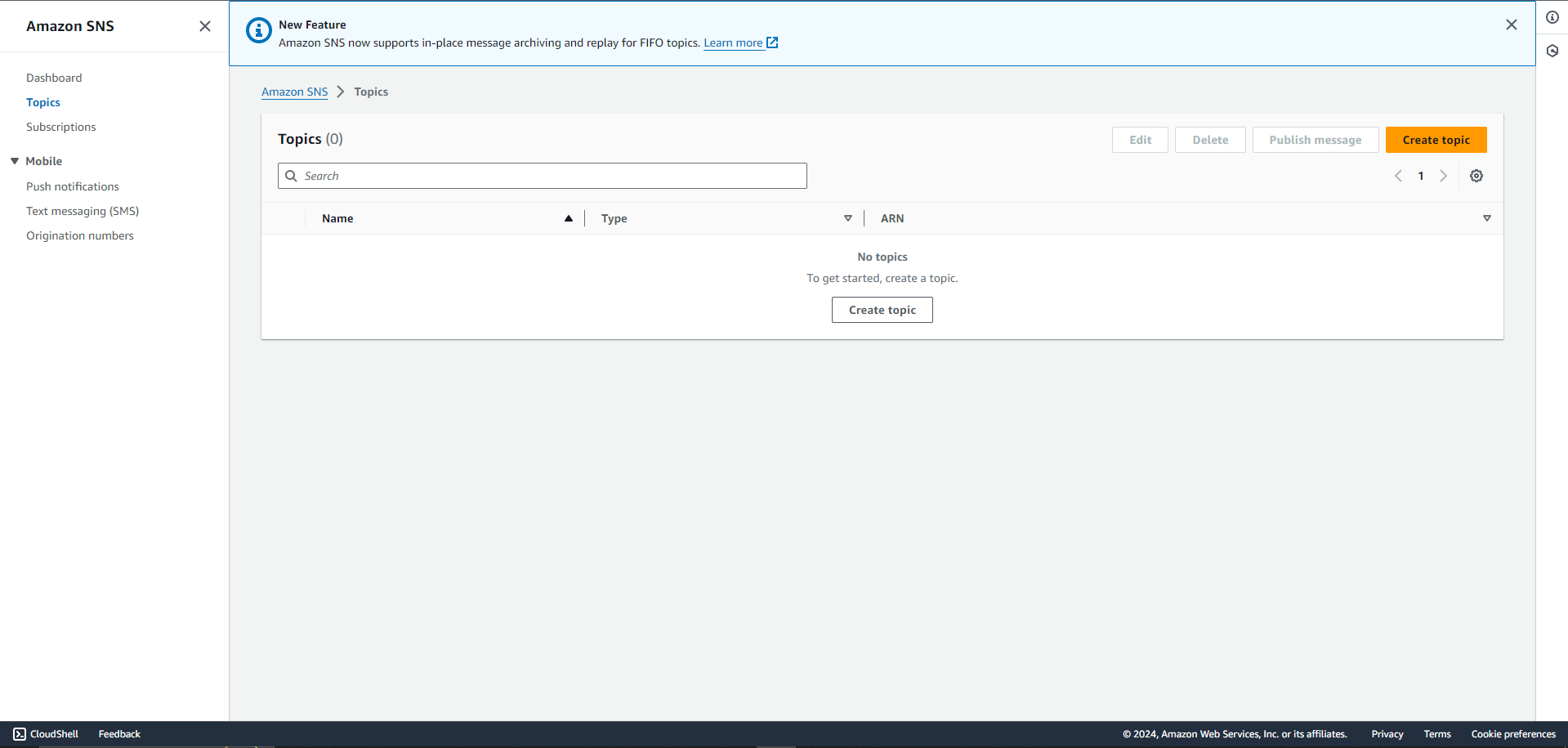
Click on Create topic and name your topic on the next page.
A good name goes a long way. We recommend you use a name that you and your peers can easily identify. One way is to give the topic your service's name on Palzin Monitor
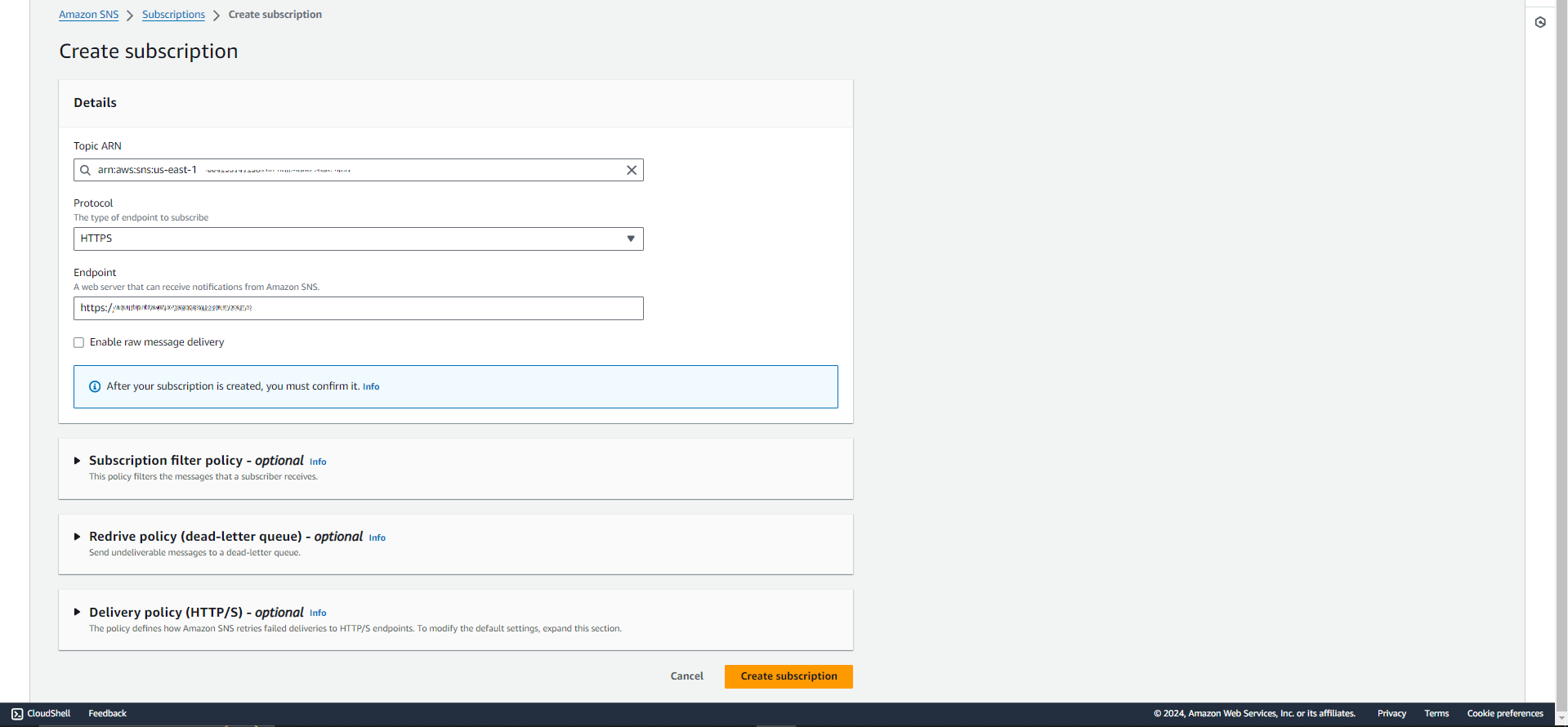
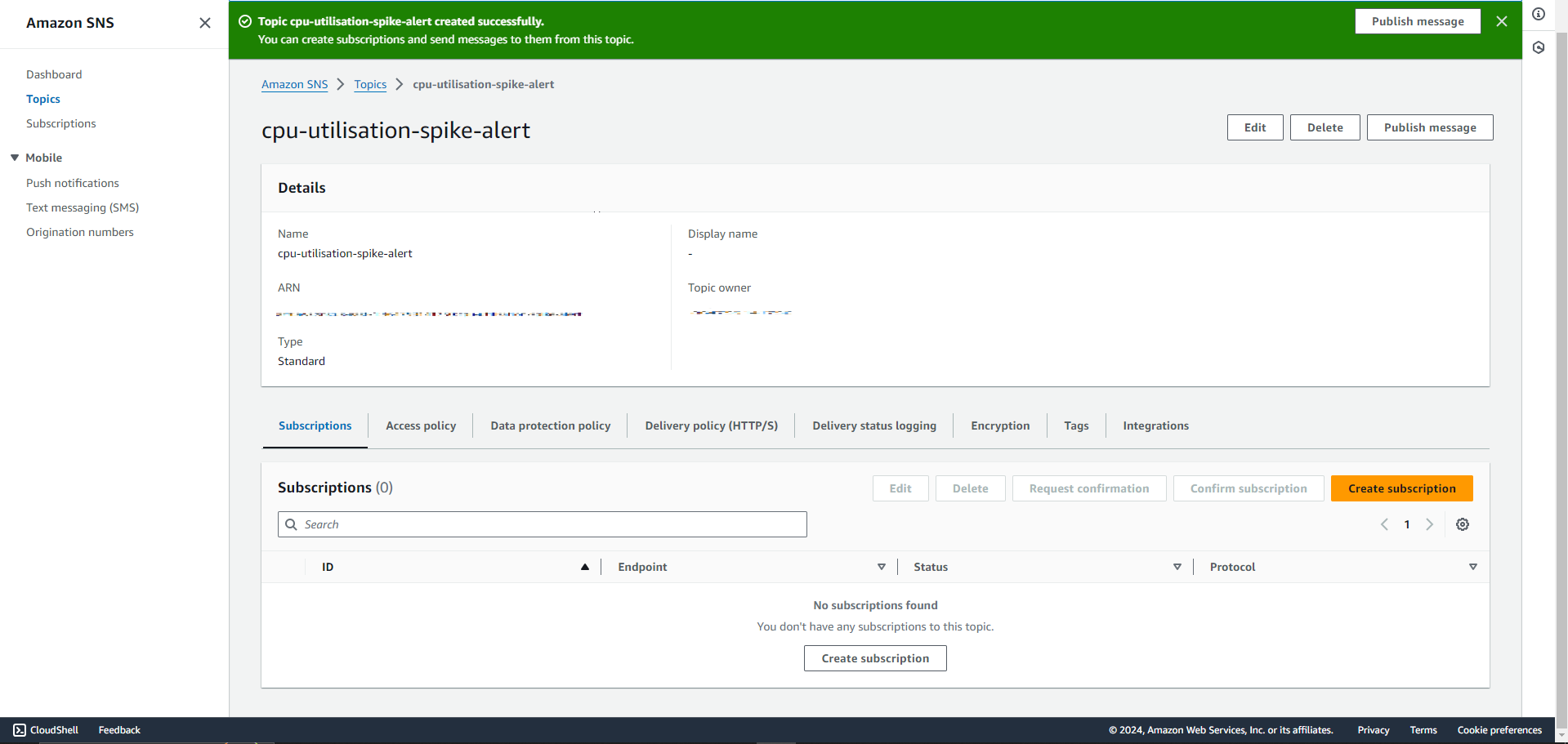
Once the topic is created, you will need to create a subscription (this is where you paste the webhook you copied from Step 1)
Once you created a topic, you will see your topic page like this
Create a subscription for the topic you create before this step
Select HTTPS as the protocol and paste the copied webhook into the endpoint and click on create subscription at the bottom. Selecting HTTPS is mandatory. Palzin Monitor will automatically confirm the subscription for you.
Make sure to Refresh the page on AWS
If the status has not changed then inside the topic, can find the subscription. Select it and request for confirmation.
We will use the above topic to receive incidents by creating alarms on Cloudwatch. We will also dive into setting up incident alarms directly from EC2.
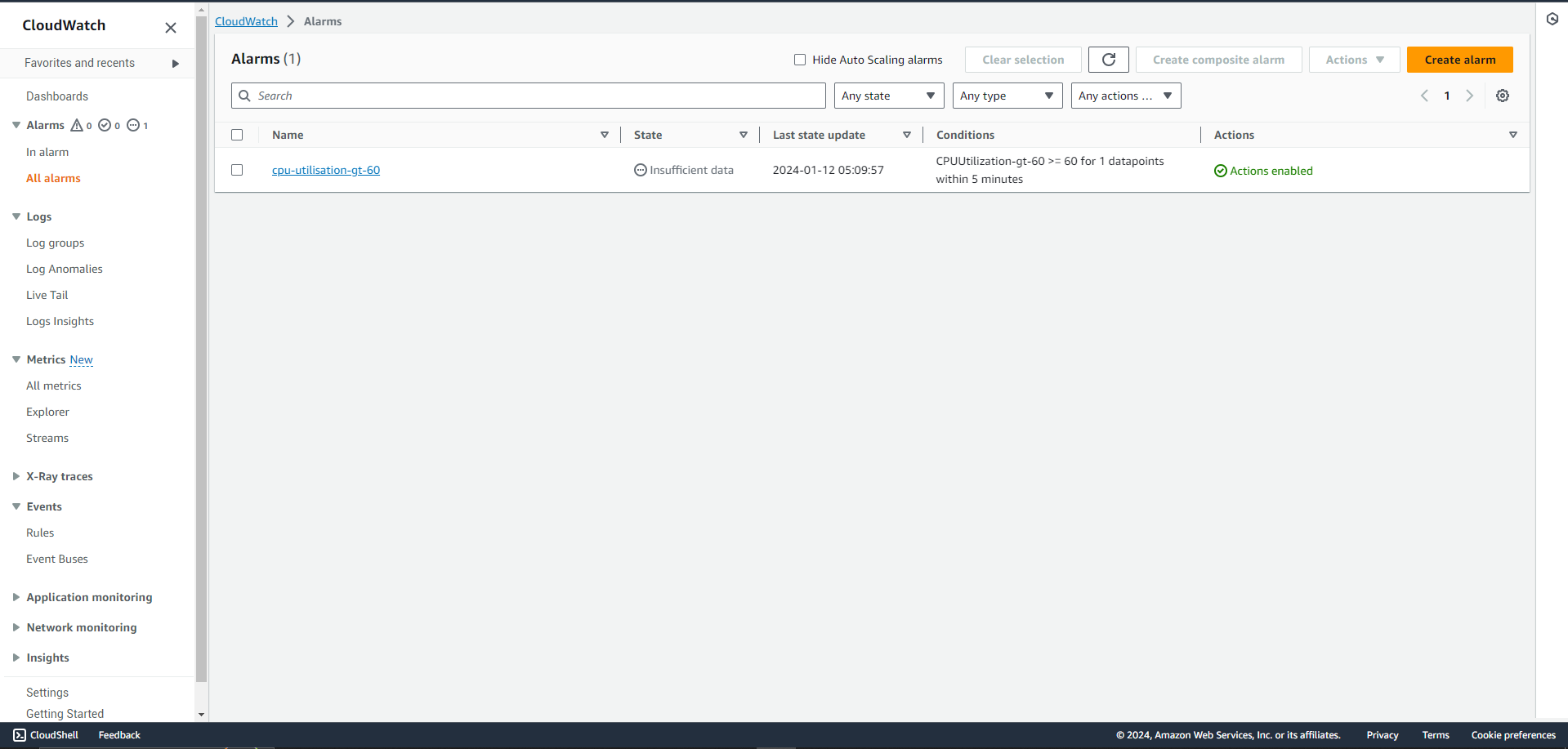
Navigate to Cloudwatch on your AWS console
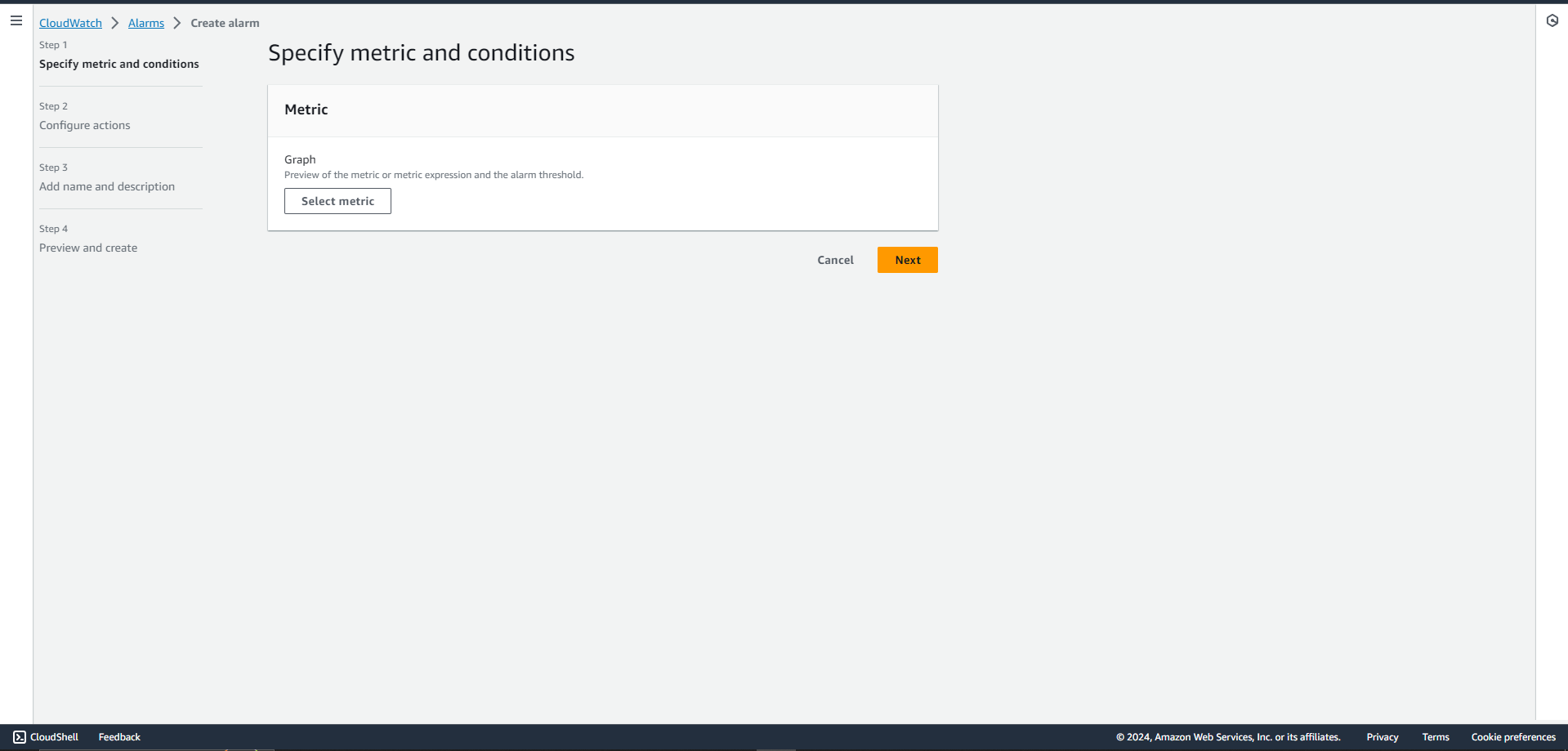
Select alarms and then create alarm
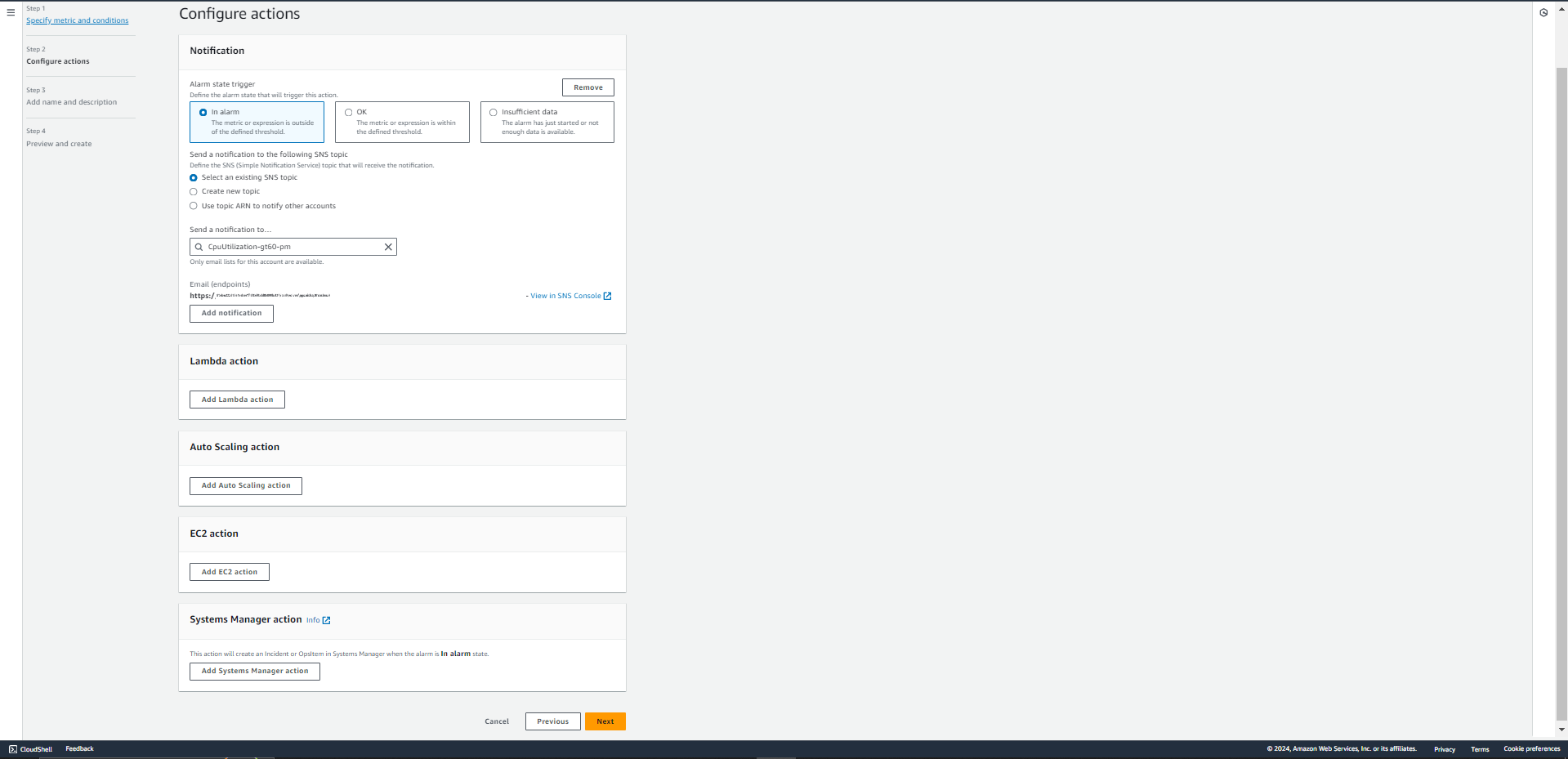
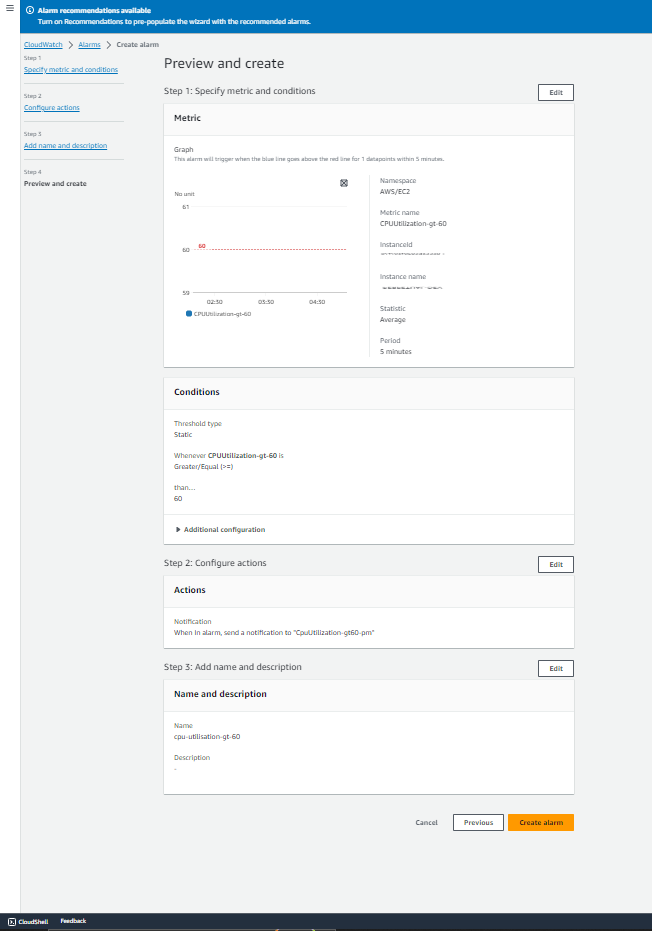
We recommend you select an alarm which is BAD. This will trigger and actually register a new incident. Palzin Monitor is soon bringing in support for OK and GOOD state.
Make sure to choose the newly created service at the bottom in the ACTIONS section.
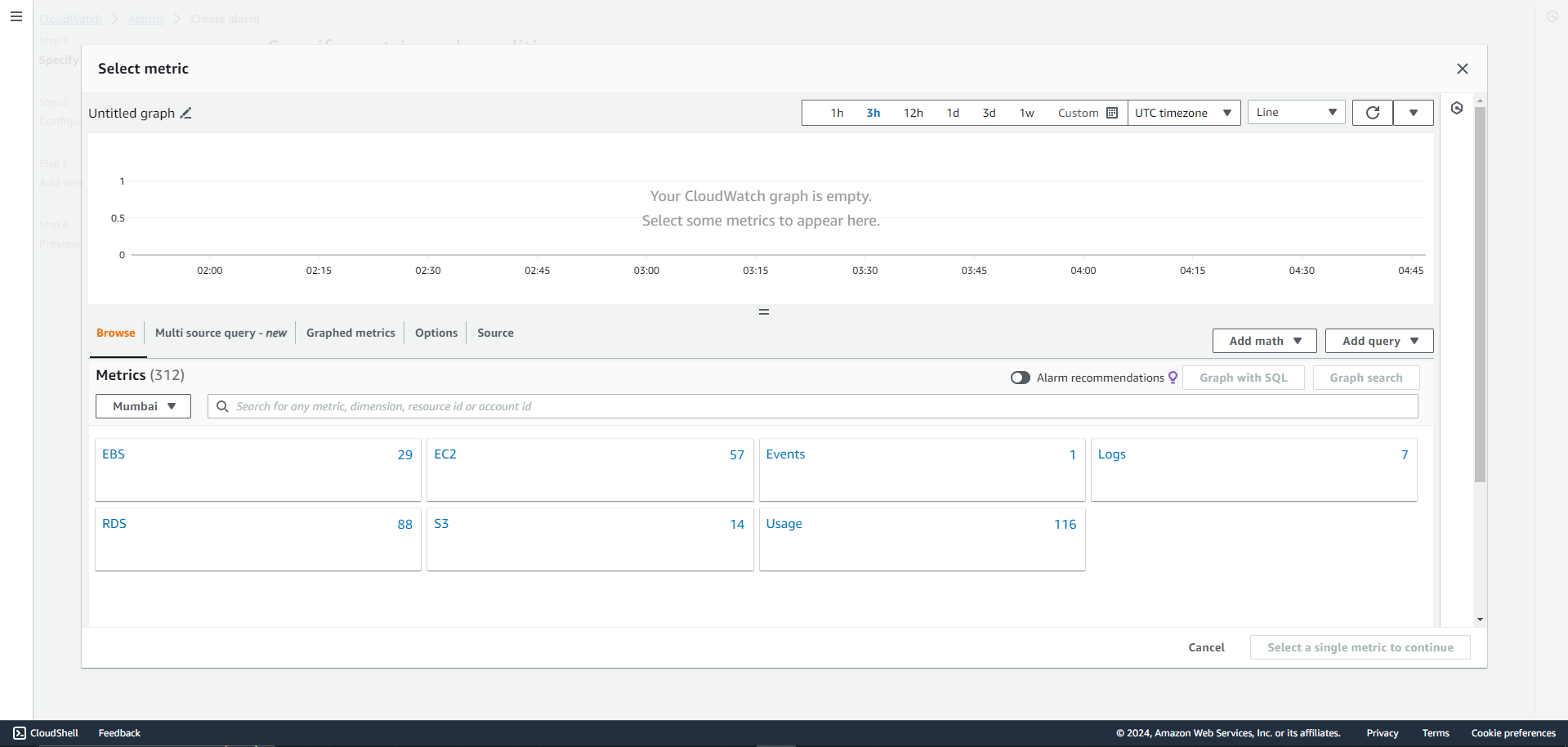
When you click on choose metric, you might see more or less services than our dashboard and that is completely fine. Choose as and many metrics you would like.
We recommend choosing many metrics as incidents can occur from any of the above services including billing.
This integration supports auto resolution by adding an OK state in all your monitors in AWS
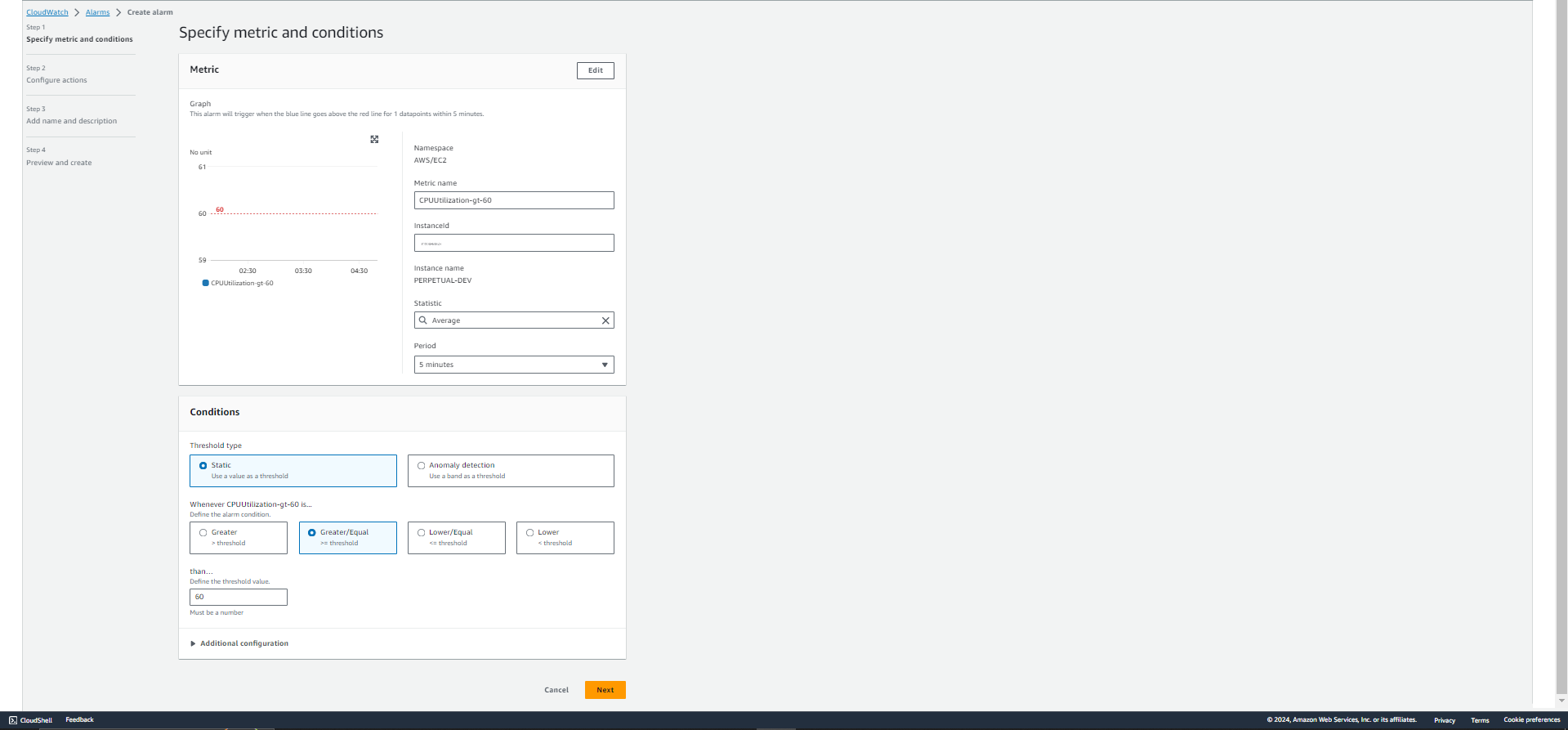
We will setup incident alerts for EC2 as an example here -
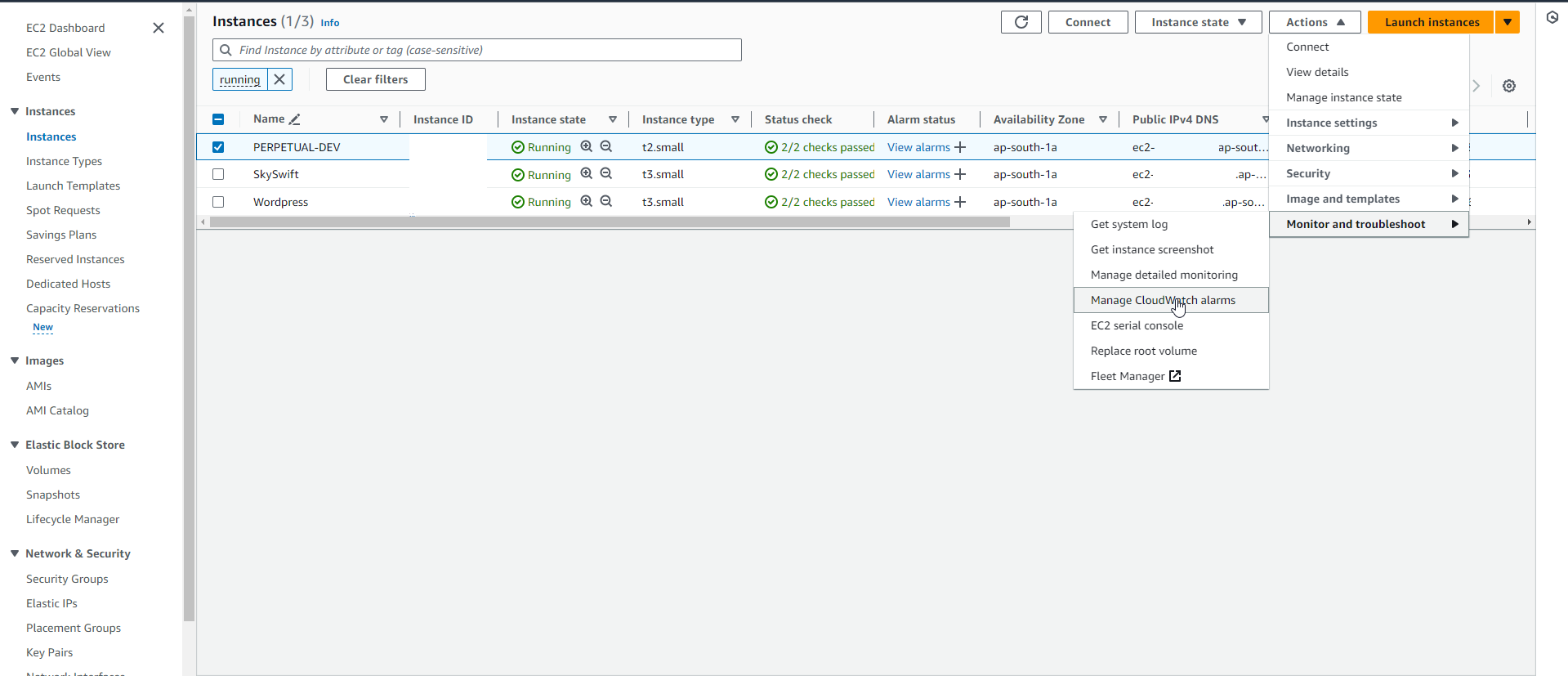
Follow these steps below once you have selected instance from sidebar on EC2 -
1.Select an instance
2.Go to Actions
3.Cloudwatch Monitoring
4.Add/Edit alarms
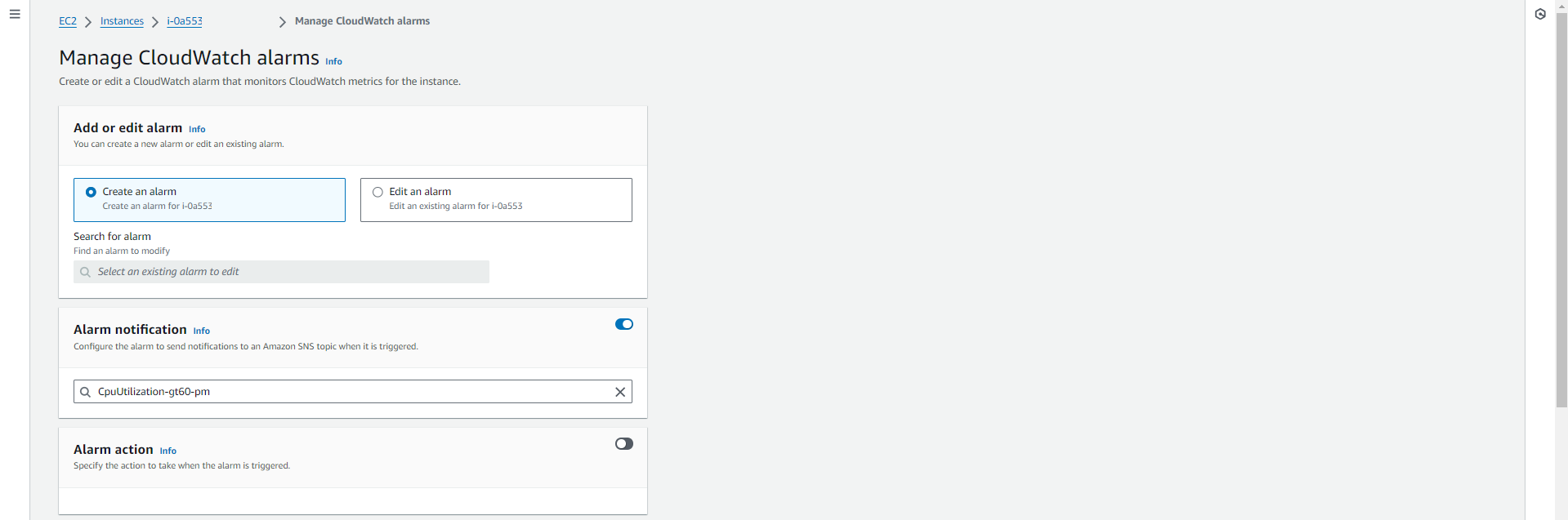
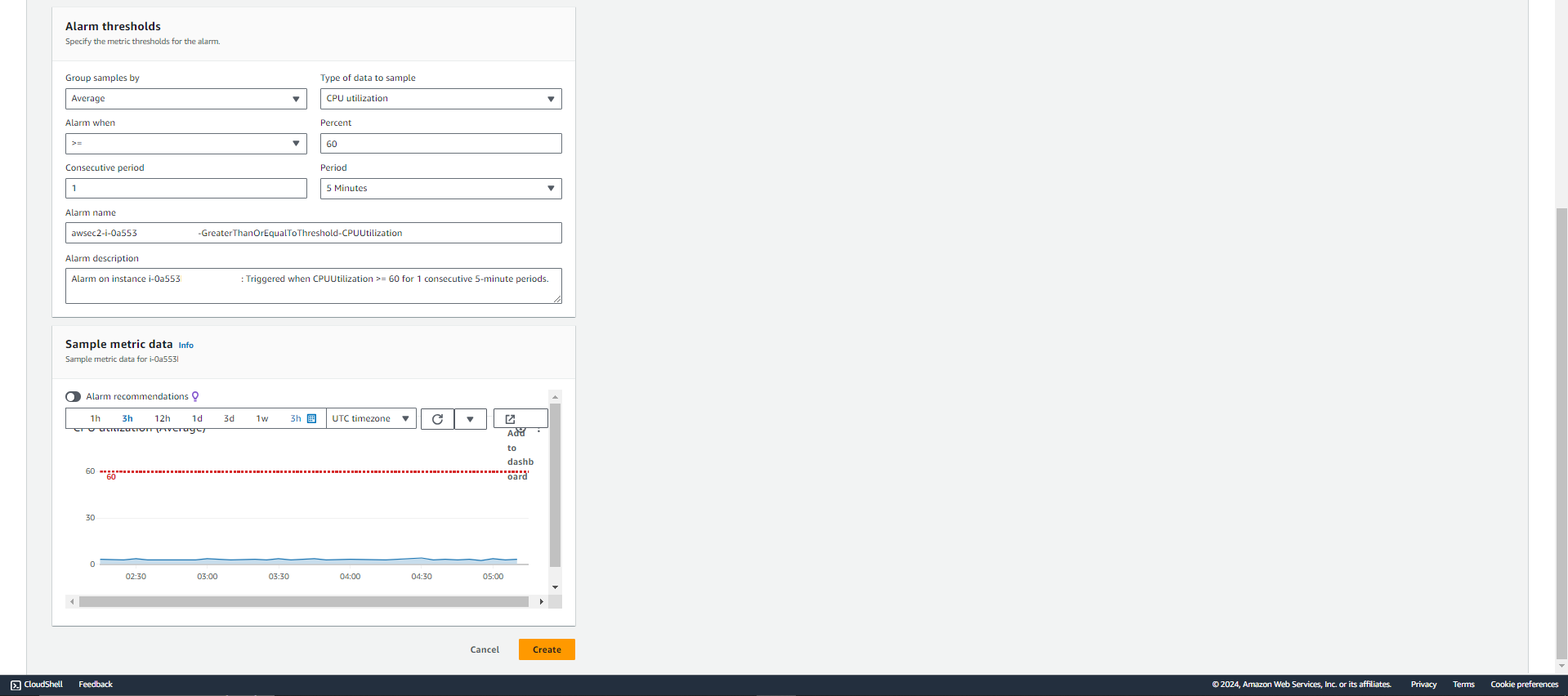
Once you see the above popup, make sure to select the SNS topic you created in Step 2. Fill in the details for your alarm.
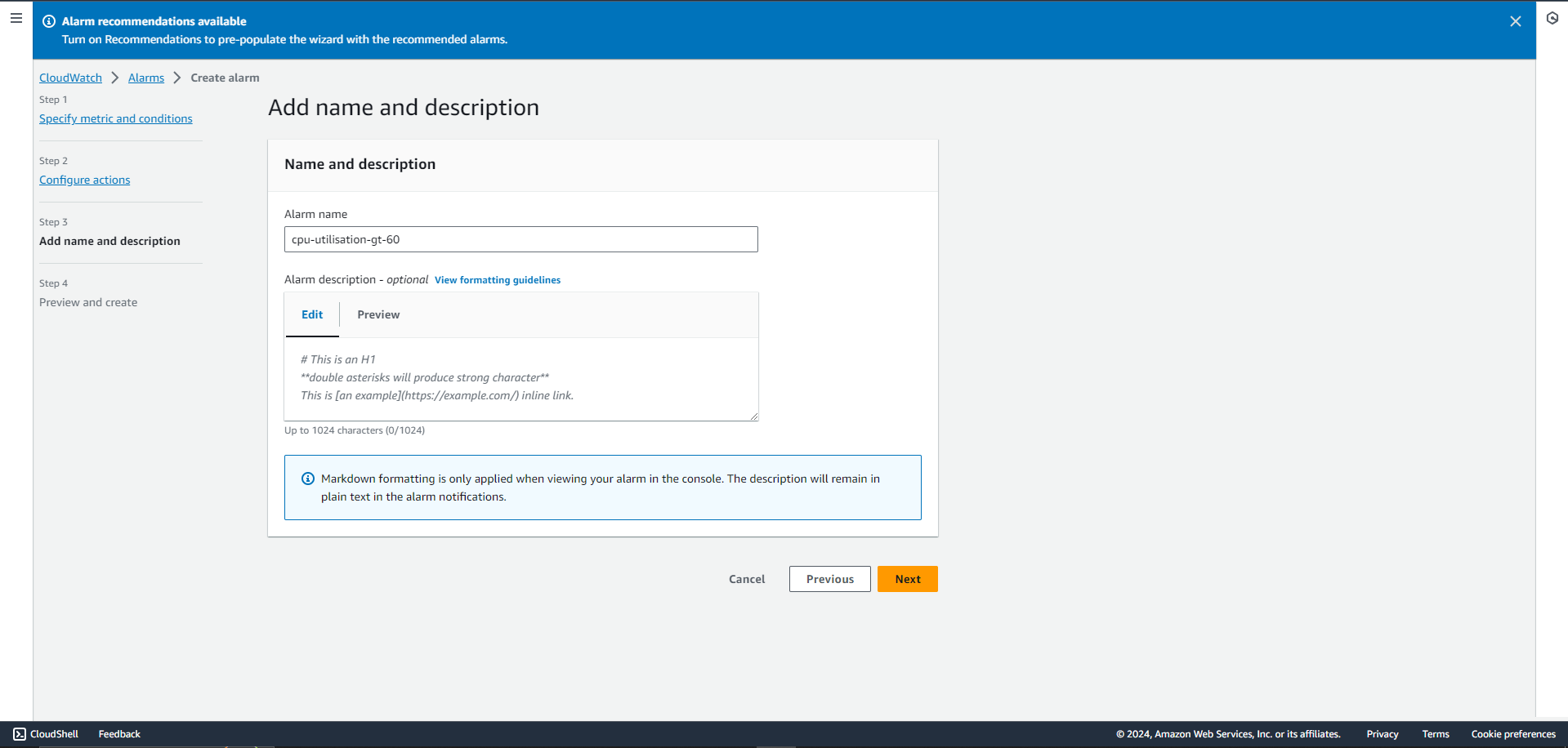
As an example, we have created a simple alarm for when the CPU Utilization crosses 60% on our EC2 instance.
1.How many services and integrations can I create on Palzin Monitor?
2.How many escalation policies can I have on Palzin Monitor?
3.How many SNS topics can I create on AWS?
At Palzin, our dedicated efforts revolve around seamless integration with the diverse range of tools utilized by your business. Our mission is to empower you in proactively detecting incidents, crashes, and performance issues, ensuring timely resolution and enhancing the customer experience.
If you have a specific integration in mind that you would like us to develop exclusively for you, we would be delighted to assist. Feel free to reach out to us at hello@palzin.app. We are here to help bring your integration ideas to life!
{
"version": "0",
"id": "12e03124-1111-asd18-12358e9",
"detail-type": "AWS Health Event",
"source": "aws.health",
"account": "sf232428agsh2",
"time": "2021-02-12T03:43:58Z",
"region": "us-east-1",
"resources": [
"arn:aws:acm:us-east-1:sf232428agsh2:certificate/*****"
],
"detail": {
"eventArn": "arn:aws:health:us-east-1::event/ACM/AWS_ACM_RENEWAL_STATE_CHANGE/AWS_ACM_RENEWAL_STATE_CHANGE-sajkj2o59273958",
"service": "ACM",
"eventTypeCode": "AWS_ACM_RENEWAL_STATE_CHANGE",
"eventTypeCategory": "scheduledChange",
"startTime": "Fri, 12 Feb 2021 03:43:58 GMT",
"endTime": "Fri, 12 Feb 2021 03:43:58 GMT",
"eventDescription": [
{
"language": "en_US",
"latestDescription": "This is to notify you that AWS Certificate Manager (ACM) has completed the renewal of an SSL/TLS certificate that certificate includes the primary domain *.test.us and a total of 1 domains.\\\\n\\\\nAWS account ID: 6871628agsh2\\\\nAWS Region name: us-east-1\\\\nCertificate identifier: arn:aws:acm:us-east-1:6871628agsh2:certificate/uiu-05dc-447e-asdhlljh-7f96db079cc2\\\\n\\\\nYour new certificate expires on Mar 13, 2022 at 23:59:59 UTC. \\\\nIf you have questions about this process, please use the Support Center at https://console.aws.amazon.com/support to contact AWS Support. If you don’t have an AWS support plan, post a new thread in the AWS Certificate Manager discussion forum at https://forums.aws.amazon.com/forum.jspa?forumID=206\\\\n\\\\nThis notification is intended solely for authorized individuals for *.test.us. To express any concerns about this notification or if it has reached you in error, forward it along with a brief explanation of your concern to validation-questions@amazon.com.\\\\n"
}
],
"affectedEntities": [
{
"entityValue": "arn:aws:acm:us-east-1:test-2417898=19998:certificate/3945231-095dc-441adsfj-9cc52"
}
]
}
}
It takes less than a minutes to setup your first monitoring.